If you are like me, you have lots of accounts, and lots of passwords. Keeping track of them all is a bit of a pain, and it’s increasingly something that you just can’t do with your brain. Several of my accounts now refuse to allow you to use a password which I consider manageable for memorization. Even if I could memorize them, you can’t reuse them for multiple accounts, so each new account places additional labor. This means that you often forget passwords, that you often have to reset them (which is a pain) and which is no real panacea for security, since if someone has access to the device or email that you receive reset notices about, they can go ahead and change them as well.
I’ve no original thinking about this: simply google “problem with passwords” and you’ll get dozens of articles about issues surrounding password security.
Most places are no ameliorating some of the worst problems with two factor authentication. The idea is that in addition to knowing the login password, you need to do something else, such as provide a separate time based, one time password generated by your mobile phone. Perhaps the most widely used of these is Google Authenticator which is an application that can be run on your phone. Many mobile applications such as Google Mail, Facebook, and WordPress can be configured to use Google Authenticator.
And it’s not a bad solution. In fact, it’s the solution that I used on my blog and many other applications for quite some time.
But it is kind of a pain. When you log in you have to stop what you are doing, dig out your phone, and then select the account you are interested in, and then manually copy the number from the app to your website or whatever. I began to wonder if there was some other sort of two factor authentication that would be simpler.
Recent models of the iPhone and MacBook have fingerprint scanners builtin. In many situations to verify your identity, you just press your thumb onto the pad, and voila. It’s very convenient.
But I wanted a simpler solution for use on my laptop, which doesn’t have a fingerprint scanner.
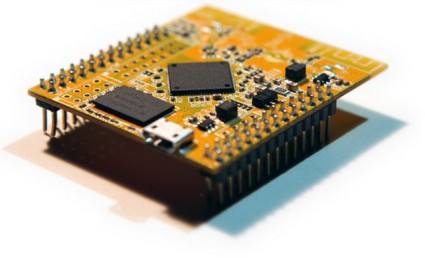
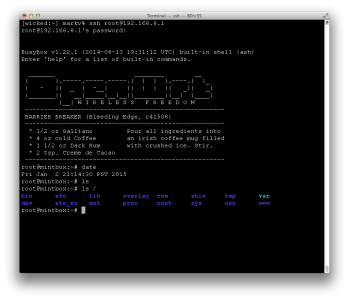
Enter the U2F Zero, a $9 USB fob you can order from Amazon.
It is a bare bones little gadget: a naked PCB that implements the Universal 2nd Factor authentication standard. This particular one is open source and very inexpensive. You can get slightly more robust and commercially supported products from Yubico (and probably others, since it is an open standard).
The idea is that you enable U2F on a website like Facebook, which will then ask you to insert your key into a USB port and click the button. This registers this device. When you next try to login, it will ask you to reinsert your key and press the button. You don’t have to copy any numbers, just one button push and you are good to go.
I’ve only had my key for a few days, and the only application that I’ve really played with is WordPress (in fact, for the very blog that you are looking at). Here are some of my early observations:
- U2F needs to be supported by your browser. I use Chrome on virtually every machine I have, which is well supported on all the platforms I commonly use. I’ve tested it on Linux and Mac OS.
- To add two factor authentication to WordPress, you need to use a plugin. I used the Two Factor plugin, by George Stephanis. This adds some additional entry to the “User Profile” section of WordPress, and allows you to enable two factor authentication in a variety of ways (via email, google Authenticator, or U2F).
- If you use U2F, then your website must use HTTPS. This was initially what spawned my switch to HTTPS several days ago, as documented here.
- You can then register your new key for the user. I initially had some difficulty with this, and traced the problem to a permissions problem in Linux. You need to make sure that the udevfs recognizes the key appropriately. You can find the directions here on github. (The key itself shipped with no documentation.)
- And, it works.
By no means have I done a security audit of the device. I have no real insight into how it works. It’s not clear to me how physically robust the device is, or whether it represents a significant improvement over just using Google Authenticator. I will continue to play with it for now. One of the things on my list is to implement a webserver of my own in Python that uses the U2F protocol as well. Eventually I’ll try it with other applications (github probably next) but will probably continue to use Google Authenticator for many others.
If you are interested in this topic, feel free to leave a comment or ask a question.
Addendum: The github page for the U2F Zero indicates that the CPU it uses is a “Universal Bee” which is made by Silicon Labs, which cost about $1.38 in quantity one, and are optimized for low power USB applications. It has 16K of flash memory, and 2K of RAM.